// Computer Engineering · ENISO · Tunisia · Class of 2027
Oussama
Ghali
Cybersecurity Engineer · SOC Builder · CTF Competitor
Defensive monitoring meets offensive testing — building secure systems,
analyzing threats, and automating security workflows with AI.
Now featuring live profile ID and mission status
// 01 · About
Who Am I?
// 02 · Experience
Field Work
- Deployed SIEM monitoring multiple endpoints — generated and analyzed 100+ security alerts from simulated attack scenarios
- Detected brute-force, privilege escalation, and suspicious process execution patterns
- Tuned detection rules to reduce noise and improve alert relevance during testing
- Performed log correlation across system, auth, and network events to reconstruct attack timelines
- 50+ hands-on challenges covering web exploitation, Linux privesc, and network enumeration
- Applied real-world recon → exploitation → post-exploitation methodology on vulnerable systems
- Sharpened analytical speed under time-constrained, competitive scenarios
- Coordinated cybersecurity workshops and events impacting 50+ students
- Led internal organization, communications, and execution of technical sessions and CTF prep
// 03 · Projects
Featured Work
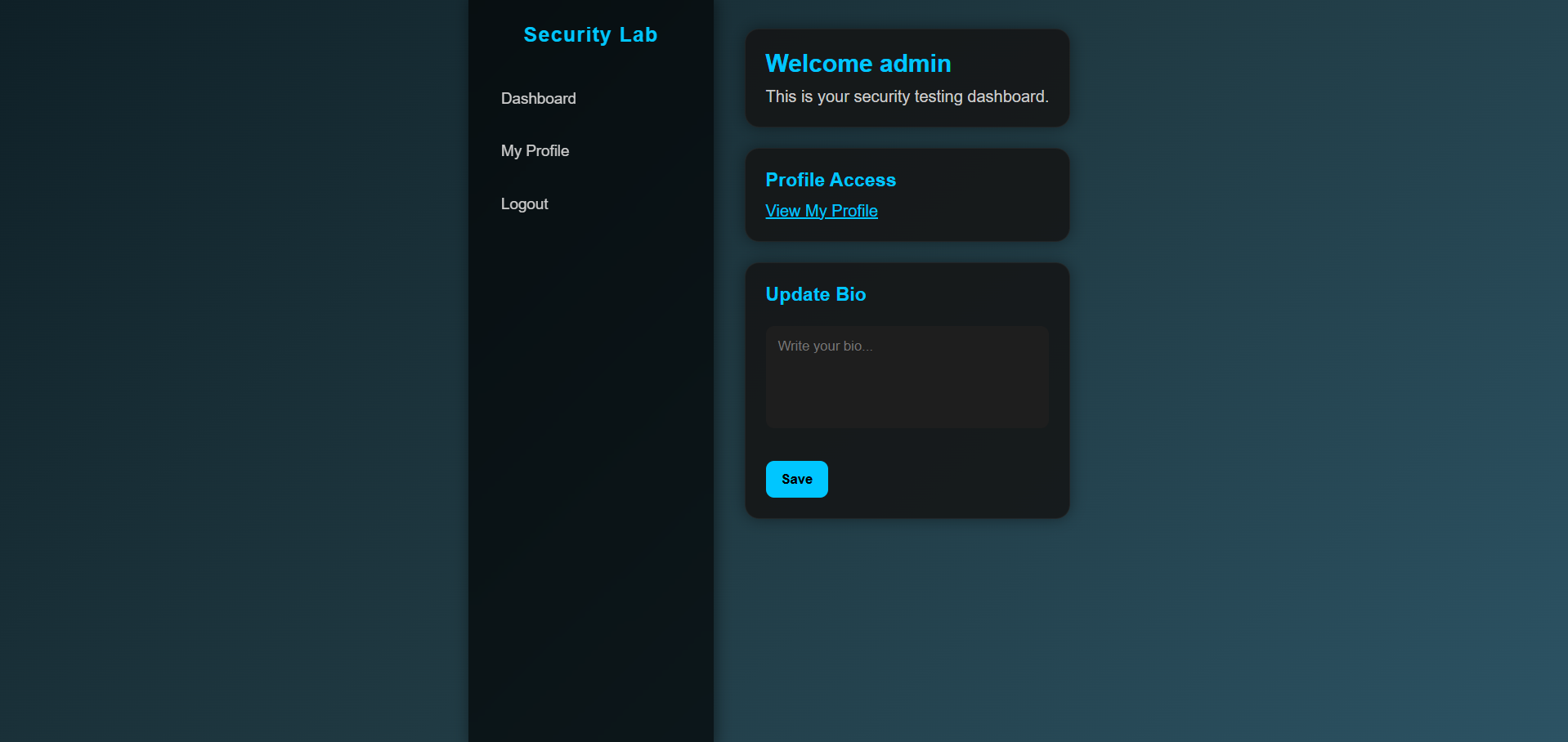
- Attack scenarios implemented: SQL Injection, XSS payload injection, and IDOR access bypass.
- Detection scenario: suspicious input patterns and auth/resource events correlated for analysis.
- Defense scenarios documented: parameterized queries, output encoding, and authorization checks.
// 04 · Skills
Arsenal
// 05 · Contact
Let's Connect
Looking for a
cybersecurity internship.
SOC analyst, blue team, or offensive security roles —
ready to contribute from day one with real hands-on skills.
Currently seeking a cybersecurity internship opportunity where I can apply SIEM, offensive testing, and AI automation skills in a real security environment.
Send Message